The Empty Quadrant
An Architectural Analysis of Verification-First Blockchain Design
Research Paper • February 2026
Abstract
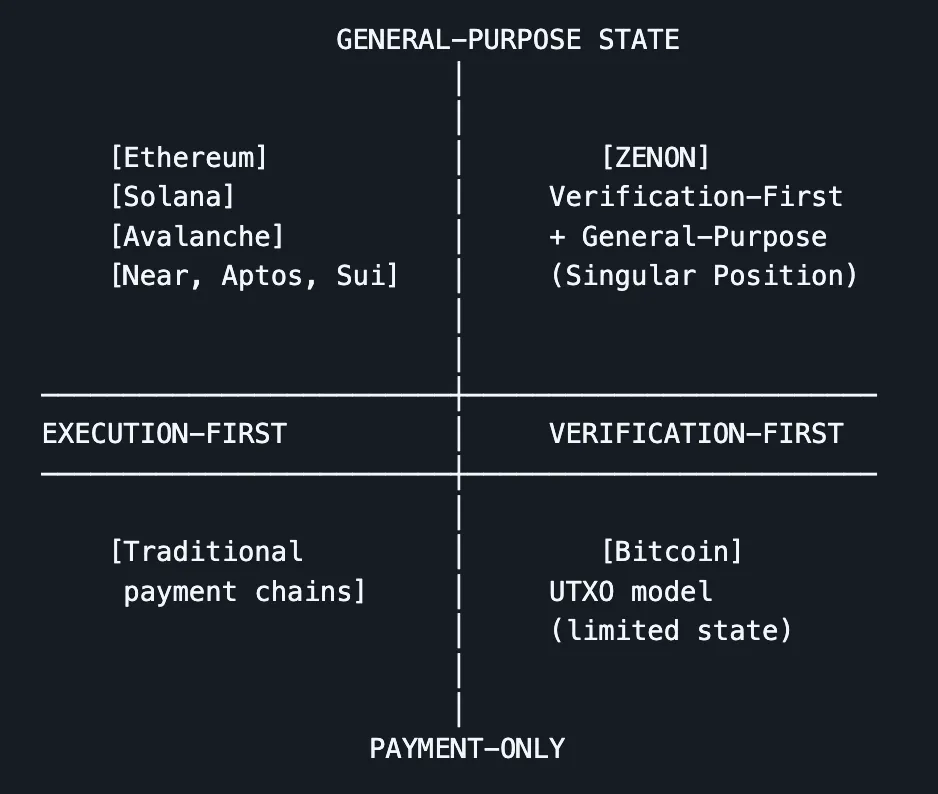
This paper examines a structural question in blockchain architecture: what component produces canonical truth in a decentralized system. It distinguishes between execution-first architectures, where global execution defines state, and verification-first architectures, where ordering defines canonical truth and execution is optional and local. Using this framework, the paper maps existing systems along two axes—execution versus verification and payment-only versus general-purpose state—revealing that the quadrant corresponding to verification-first, general-purpose base layers is effectively unoccupied in production, with Zenon as the only known instance as of 2026.
The analysis demonstrates that this empty quadrant is not the result of oversight or insufficient capital, but of architectural irreversibility. Once a network launches with execution as the source of truth, the economic, compositional, and security assumptions of the ecosystem create incompatible invariants with verification-first design. No known migration path exists that preserves existing contracts, liquidity, or composability. These incompatibilities are formalized as invariant conflicts in Appendix A. Conversely, a verification-first base layer can add execution capabilities without altering what produces canonical truth.
The paper concludes by examining why structurally sound architectures can remain underutilized when tooling and developer mental models lag behind design, and outlines the conditions under which verification-first architectures could be replicated—emphasizing that doing so requires genesis-level reconstruction with a multi-year timeline to maturity.
Executive Summary
The Core Question
What produces canonical truth in a blockchain: execution or ordering?
The Framework
Two architectural classes exist, defined by protocol-enforced invariants:
-
EXECUTION-FIRST: Canonical state ≡ result of globally agreed execution
- Invariant: Light clients must trust execution results or re-execute to verify state
- Examples: Ethereum, Solana, Avalanche, most L1s
-
VERIFICATION-FIRST: Canonical truth ≡ cryptographically ordered transaction set
- Invariant: Light clients verify ordering; execution is optional and local
- Examples: Bitcoin (payment-only), Zenon (general-purpose state)
The Empty Quadrant
Mapping systems by [execution vs. verification] × [payment vs. general-purpose state] reveals one effectively unoccupied territory: verification-first + general-purpose state.
Why this matters: The architectural choice determines:
- Whether verification cost scales with execution complexity
- Whether composability requires global atomic execution
- Whether security models are integrated or composite
- Whether light clients can verify without trusting remote infrastructure
The Irreversibility Thesis
The relationship between execution and canonical truth cannot be inverted post-genesis because the invariants are incompatible:
| Dimension | Execution-First | Verification-First | Migration Blocker |
|---|---|---|---|
| Truth source | Executed state roots | Ordered transaction set | Contract addresses, wallet assumptions |
| Verification | Re-execute or trust proofs | Verify ordering signatures | Light client architecture |
| Composability | Synchronous, atomic | Asynchronous, message-passing | Application dependencies |
| Security | Composite (DA + execution + bridges) | Integrated (single consensus) | Layer decomposition impossible |
| Validator economics | Execution throughput rewards | Ordering finality rewards | Incentive realignment breaks existing model |
Necessary condition for migration: Breaking all existing applications, contracts, and tooling. Sufficient condition: Launching an entirely new network.
These constraints are formalized as incompatible invariants in Appendix A.
Falsifiability
This framework is falsifiable. A production system would constitute a counterexample if it:
- Demonstrates material economic activity (>$100M TVL or >10K daily active users)
- Satisfies all four verification-first criteria simultaneously:
- Ordering alone produces canonical truth (consensus does not require execution agreement)
- Execution is optional and local (interested parties execute only relevant state)
- Light clients verify ordering directly (no trust in execution proofs or remote infrastructure)
- Single integrated security model (no composite layering with distinct trust assumptions)
- Supports general-purpose stateful computation (not limited to payment-only use cases)
- Has operated continuously for >1 year without consensus failures
As of February 2026, no system beyond Zenon satisfies all four conditions simultaneously.
Implications
- Execution-first systems can reduce verification costs (ZK proofs, stateless clients) but cannot make ordering the source of truth
- Verification-first systems can add execution layers without changing what produces canonical truth
- Genesis-level architectural commitments are permanent
- The empty quadrant can only be filled by new network launches, not upgrades
Open Questions
- Will verification costs rise faster than hardware improvements?
- Will markets value trustless verification over convenience?
- Can verification-first ecosystems develop tooling that matches execution-first maturity?
Not Claimed
- That verification-first will achieve market dominance
- That execution-first is architecturally incorrect
- That any specific network will succeed commercially
This is architectural analysis, not market prediction.
Table of Contents
- Introduction
- Architectural Taxonomy
- The Empty Quadrant
- The Irreversibility Thesis
- Attempts to Approximate Verification-First
- Development Reality and Interpretation Gap
- Genesis-Level Reconstruction
- Strategic Implications
- Addressing Counterarguments
- Conclusion
Preface
This paper is not a proposal, a roadmap, or an argument for adoption.
It is an architectural analysis.
The motivation is simple: blockchain discourse increasingly discusses verification—stateless clients, proofs, rollups, modular stacks—without clarity about what produces canonical truth in the system. This paper examines that question by distinguishing between execution-first and verification-first as structural properties enforced by protocol behavior, not marketing terms.
From this lens, it becomes possible to map existing systems, identify architectural territory, and reason about which transitions are possible and which are incompatible with existing invariants.
Zenon appears as an empirical reference point: a production system exhibiting verification-first properties for general-purpose state. The paper makes no claims about designer intent beyond what protocol behavior demonstrates.
This analysis does not predict market outcomes. Architectural correctness and market dominance are orthogonal. The purpose is to clarify a distinction, explain why it is irreversible once chosen, and document implications for existing networks and future designs.
Readers should approach this as a framework—one intended to remain useful regardless of which networks ultimately succeed.
Reader’s Guide
For protocol designers and L1 architects
Focus on:
- Sections 2–4 (Taxonomy, Empty Quadrant, Irreversibility Thesis) — core technical argument
- Section 9 (Counterarguments) — addresses strongest objections
- Appendix A (Formal Definitions) — invariants and necessary/sufficient conditions
For researchers and systems theorists
Focus on:
- Sections 2–3 (problem space definition)
- Section 8 (Strategic Implications) — long-run evolution framing
- Appendix A — formalization of incompatibility claims
For developers and ecosystem builders
Focus on:
- Section 6 (Interpretation Gap) — why architectural capability ≠ usable systems
- Section 7 (Genesis-Level Reconstruction) — tooling alignment requirements
For skeptics
Focus on:
- Section 2 (precise definitions, no intent-based arguments)
- Section 4 (concrete incompatibility claims, formalized in Appendix A)
- Falsifiability criteria (Executive Summary, Section 3)
- Section 9 (steelman counterarguments)
- Conclusion (explicit limitations)
How not to read this paper
- Not a prediction of market winners
- Not a claim of inevitability
- Not a critique of execution-first as “wrong”
Execution-first architectures succeeded by optimizing for historically valued properties. This paper argues those optimizations carry irreversible constraints.
Suggested reading order (time-constrained)
- Abstract + Executive Summary
- Sections 2–3 (Taxonomy + Empty Quadrant)
- Section 4 (Irreversibility Thesis)
- Section 9 (Counterarguments)
- Conclusion + Appendix A
1. Introduction
As verification-first blockchain architectures have become easier to describe, a natural concern emerges: do visible architectural principles cease to be advantages? If documented and diagrammed publicly, why wouldn’t better-funded teams replicate them?
This concern is well-founded. In cryptocurrency history, pioneers are often overtaken. Ethereum didn’t invent smart contracts. Bitcoin didn’t invent digital cash. First movers rarely capture majority value.
This paper addresses that concern by examining what replication requires. The core claim is about time and irreversibility: some architectural commitments made at genesis cannot be reversed without relaunching entirely.
The central question: can an execution-first network pivot to verification-first architecture where ordering, not execution, produces canonical truth?
The argument: No. Not because of absent will, but because the invariants are incompatible (formalized in Appendix A as structural constraints on continuous system transformations).
2. Architectural Taxonomy
This analysis treats verification-first and execution-first as structural categories defined by protocol-enforced properties, not intent or marketing.
Definition: Verification-First System
A system is verification-first if and only if it satisfies all four properties:
-
Ordering produces canonical truth (not execution)
- Necessary condition: Transaction ordering is sufficient to determine canonical history
- Sufficient condition: Any party can derive state by replaying ordered transactions locally
-
Execution is optional and local (not mandatory and global)
- Necessary condition: Consensus does not require global execution agreement
- Sufficient condition: Interested parties execute only relevant state transitions
-
Light clients verify ordering directly (not execution proofs)
- Necessary condition: Verification requires checking cryptographic ordering (signatures, consensus votes, PoW links)
- Sufficient condition: State queries require no trust in remote execution
-
Integrated security model (not composite layering)
- Necessary condition: Single consensus mechanism secures both ordering and truth
- Sufficient condition: No separate security assumptions for different system layers
Definition: Execution-First System
A system is execution-first if:
-
Canonical state ≡ globally agreed execution results
- Consensus reaches agreement on executed state roots, not just transaction ordering
-
Verification fundamentally requires execution confirmation
- Either by re-execution or by validating cryptographic proofs of execution correctness
Classification principle: Observable protocol behavior determines category, not designer vocabulary. A whale is a mammal because it exhibits mammalian properties—whether it “intended” to be a mammal is irrelevant.
These definitions are formalized as invariant requirements in Appendix A.1.
3. The Empty Quadrant
Blockchain architectures occupy a two-dimensional space:
- Horizontal axis: Execution-first ← → Verification-first
- Vertical axis: Payment-only ← → General-purpose state
This yields four quadrants, three of which are well-populated in production:
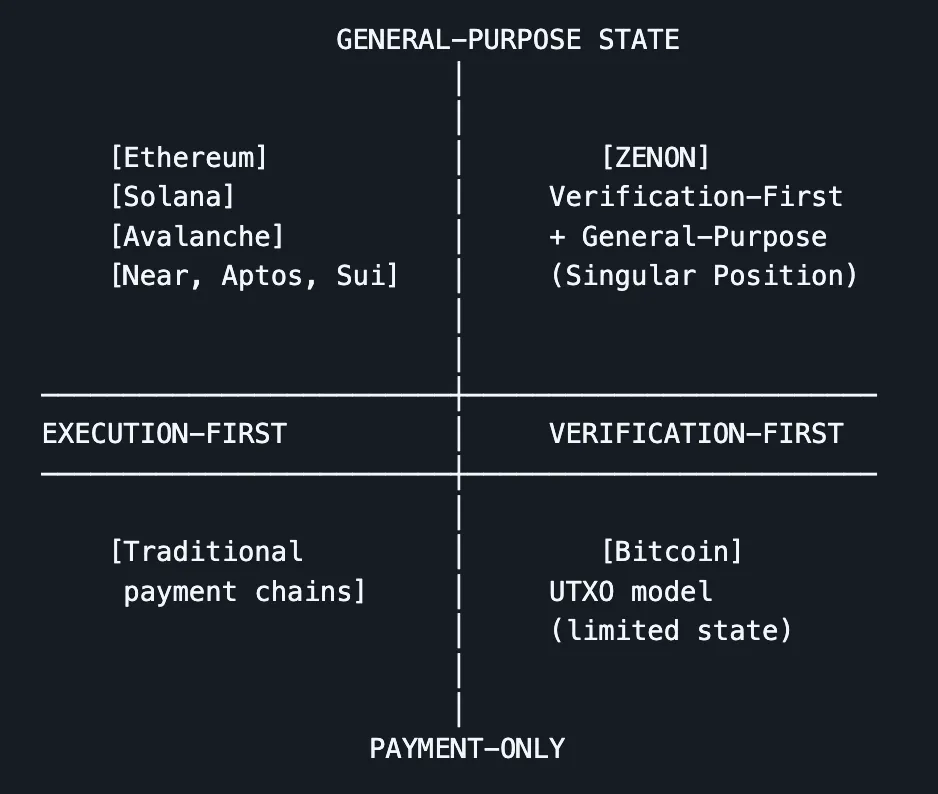
Quadrant Analysis
Q1: Execution-first, payment-only — Traditional payment chains coupling ordering and execution for value transfer only.
Q2: Execution-first, general-purpose — Ethereum, Solana, Avalanche, Cardano, Near, Aptos, Sui. Canonical state derives from globally agreed execution.
Q3: Verification-first, payment-only — Bitcoin’s UTXO model. Light clients verify transaction ordering and validity without executing a global state machine.
Q4: Verification-first, general-purpose — As of 2026, occupied only by Zenon. No other production network with material economic activity demonstrates the full combination: ordering as canonical truth, optional local execution, direct light-client ordering verification, integrated security model, general-purpose stateful computation.
Falsifiability Criteria
This claim is falsifiable. A system would constitute a valid counterexample if it simultaneously satisfies:
Empirical threshold: Material economic activity, defined as either:
- Total Value Locked (TVL) >$100M USD, or
- Daily Active Users (DAU) >10,000, or
- Transaction volume >100,000 per day sustained over 90 days
Architectural criteria: All four verification-first properties from Section 2:
- Ordering produces canonical truth (consensus finalizes transaction order, not executed state roots)
- Execution is optional and local (light clients do not need to execute or trust execution proofs to verify canonical history)
- Light clients verify ordering directly via cryptographic proofs (signatures, consensus votes, PoW/PoS proofs)
- Integrated security model (single consensus mechanism, not composite stack with separate DA/execution/bridge security)
Functionality requirement: General-purpose stateful computation (not restricted to payment-only transactions)
Operational maturity: Continuous operation >1 year without consensus failures or network halts requiring hard forks
What would disprove this framework:
- Discovery of a production system meeting all criteria above that was overlooked in this analysis
- Successful continuous migration of an execution-first system to verification-first while preserving >80% of existing application functionality
- Modular stack architecture demonstrating integrated security properties equivalent to verification-first base layer
As of February 2026, no system beyond Zenon satisfies all criteria simultaneously. This is an observational claim subject to empirical falsification.
Edge Case Examination
Cardano’s eUTXO: More expressive than Bitcoin’s UTXO, but canonical state still emerges from globally executed script validation. Light clients must trust execution or re-execute. Remains execution-first despite localized execution properties.
Actor-model blockchains: Theoretical local execution properties exist, but production implementations require global agreement on execution results for cross-actor interactions. Where atomic composability is sacrificed, general-purpose state functionality is limited.
Cosmos app-chains: Architectural possibility exists for verification-first custom state machines. Production adoption as of 2026: overwhelmingly execution-first (CosmWasm, custom VMs where execution defines state).
DAG-based systems (2025–2026 launches): BlockDAG presales, Kaspa extensions, experimental throughput testnets—all maintain global agreement on executed state. DAG topology ≠ verification-first architecture. What matters: does canonical truth derive from ordering or executed state roots?
Modular/sovereign rollups: Theoretical architectural flexibility exists at application layer. Production deployments: dominated by execution-first patterns where settlement layers or fraud/validity proofs anchor state to executed results.
Why Bitcoin Cannot Fill This Quadrant
Bitcoin demonstrates verification-first properties for payments because state is minimal and local. Each UTXO is independent—verifying ordering suffices to determine spendable outputs.
General-purpose state introduces:
- Complex cross-contract dependencies
- Composability requirements (multi-contract interactions within transactions)
- Arbitrary computation beyond simple script validation
Achieving verification-first properties for general-purpose state requires architectural commitments Bitcoin’s payment-focused design doesn’t make.
4. The Irreversibility Thesis
Central claim: Once a network launches with execution as the source of canonical truth, it cannot pivot to verification-first without complete reconstruction because the invariants are incompatible across five dimensions (formalized in Appendix A.2 as constraints on continuous transformations).
Once a network launches with execution as the source of canonical truth, it cannot pivot to verification-first without complete reconstruction.
4.1 Structural Incompatibility
Execution-first invariant: Ordering and execution share substrate. Transactions ≡ state transitions in global state machine. Consensus ≡ agreement on executed state roots.
Verification-first requirement: Dual-ledger separation. Ordering layer produces canonical truth. Execution layer holds optional local state.
Migration blocker: Retrofitting requires redefining transaction formats, replacing state model, redesigning VM, rewriting consensus rules. This is not an upgrade—it is launching a new network.
4.2 Canonical Truth Migration
Execution-first dependencies:
- Contract addresses derived from execution state
- Wallet integrations assume executed state roots
- Application architectures expect global atomic execution semantics
- Composability patterns rely on synchronous state transitions at block boundaries
Verification-first requirement: Ordering is truth. Execution is local derivation.
Migration blocker: No preservation path exists for ecosystem assumptions. All contracts, applications, and integrations break.
4.3 Security Model Incompatibility
Execution-first + verification features → Multi-layer composite security:
- Base layer (ordering + DA)
- Execution layer
- Bridge contracts
- Verification proof systems
Each layer: separate trust assumptions, potential failure modes.
Verification-first architecture → Integrated security:
- One consensus mechanism governs ordering
- Execution treated as optional local activity
- No trust assumptions beyond ordering consensus
Migration blocker: Decomposing composite security into integrated security requires system replacement, not layer addition.
These incompatibilities are formalized in Appendix A.2 as invariant conflicts that prevent continuous transformations between architectural classes.
4.4 Economic Incentive Lock-In
Execution-first validator economics:
- Hardware expenditure optimized for execution throughput
- Fee markets reward processing capacity
- Competitive advantages tied to execution performance
Verification-first economics:
- Consensus rewards ordering finality
- Execution no longer central to validation
- Hardware optimization shifts to ordering proof generation
Migration blocker: Existing validators’ sunk costs and competitive positions evaporate. No political or economic path to adoption.
4.5 Composability Assumptions
Execution-first composability: Synchronous atomic execution within blocks. Multiple contracts interact in single transaction with guaranteed state visibility.
Verification-first composability: Asynchronous message-passing between account chains. State updates propagate via ordered messages, not atomic execution.
Migration blocker: DeFi protocols, complex applications, and developer mental models assume synchronous composability. Architectural inversion requires complete application redesign.
Summary
The irreversibility thesis rests on incompatible invariants across five dimensions. Appendix A formalizes these as constraints preventing continuous transformations from execution-first to verification-first while preserving application functionality. The only viable path is discontinuous: launching a new network with verification-first commitments from genesis.
5. Attempts to Approximate Verification-First
When teams adopt verification-first ideas without genesis-level commitment, three outcomes emerge:
5.1 Execution-First + Verification Add-Ons
Approach: ZK-SNARKs for validity proofs, stateless client techniques, Verkle trees, state expiry.
Result: Verification becomes cheaper. Execution remains the arbiter of canonical state.
Assessment: Valuable efficiency improvements within execution-first framework. Does not invert what produces truth.
Examples: Ethereum stateless roadmap, ZK rollup validity proofs.
5.2 Modular Stacks
Approach: DA layer provides ordering. Separate execution layers produce application state with fraud/validity proofs.
Result: Scalability through specialization. Canonical truth about application state still resides in executed state roots on execution layers. Security model becomes composite.
Assessment: Pragmatic response to execution-first scaling limits. Not equivalent to integrated verification-first base layer (see Appendix A.3 for formal counterexample).
Examples: Celestia + rollups, Ethereum as DA + L2 environments, sovereign rollups.
5.3 Hybrid Retrofits
Approach: Bolt account-chain or dual-ledger terminology onto execution-first base.
Result: Added complexity without architectural inversion. Execution still happens globally, reintroducing verification-first problems.
Assessment: Marketing layer, not structural change.
Key Distinction
Improving verification cost ≠ inverting relationship between execution and truth.
As of 2026, no production system has retrofitted full verification-first properties (ordering as truth, optional execution, direct light-client verification, integrated security) onto an execution-first base without compromising core criteria.
6. Development Reality and Interpretation Gap
A system can be structurally correct but socially unintelligible. Architectural capabilities can exist for years before ecosystems learn to use them.
The Circular Dependency
Current verification-first ecosystems face:
- Developers don’t build verification-first apps → tooling and documentation are scarce
- Tooling doesn’t emerge → limited demand
- Demand remains low → architectural advantages aren’t visible in deployed applications
Historical Parallels
TCP/IP vs OSI: Simpler architecture eventually dominated, but OSI had stronger institutional support for years. Technical superiority required time to gain conceptual clarity.
Microkernel OS: Architecturally clean (Mach, L4) remained niche for decades despite theoretical advantages. Ecosystem and tooling gaps prevented adoption.
Public key cryptography: Invented 1970s, widely deployed 1990s when standards, libraries, and mental models caught up.
Breaking the Loop
Requires:
- Clear articulation of architectural philosophy (this paper attempts)
- Reference implementations showcasing verification-first patterns
- Tooling making account-chain and asynchronous design natural
Until these emerge, verification-first advantages remain latent rather than realized.
Zenon’s Current State (2026)
Protocol: Continuous mainnet operation since 2019. No consensus failures. Functional dual-ledger infrastructure. Feeless base layer. EVM-compatible extension chain. Decentralized governance.
Ecosystem gap: Native applications exploiting verification-first properties remain limited. Developer tooling for asynchronous account-chain patterns is immature. Comprehensive documentation incomplete.
Interpretation: Architecture preceded shared language to describe it. Developers familiar with execution-first platforms replicated familiar patterns (EVM compatibility, bridges) rather than exploiting verification-first affordances.
This illustrates a general phenomenon: protocol correctness does not guarantee ecosystem understanding.
7. Genesis-Level Reconstruction
Question: How does another team occupy the verification-first, general-purpose quadrant?
Answer: Genesis-level reconstruction only. No upgrade path exists from execution-first (proven in Appendix A.2 via invariant incompatibility).
Requirements
- Launch new network (not upgrade existing)
- Enforce dual-ledger separation from block 1
- Design all tooling around local execution, account chains, message-passing
- Accept zero continuity with execution-first ecosystems
Unavoidable Timeline
- Protocol design, testing, security hardening: 2–3 years minimum
- Decentralization of consensus participants: 1–2 years
- Governance maturation: 2–3 years
- Adversarial resilience building: 3–5 years
Meanwhile: starting from zero liquidity, applications, developer mindshare.
Second-Mover Advantages (Real but Limited)
- Visible reference implementation (codebase, design patterns)
- Proven consensus mechanisms (PoW+DPoS stability demonstrated)
- Known tooling/onboarding pitfalls
Timeline compression: None. Operational maturity and network effects aren’t compressible.
By the time new verification-first network reaches production readiness (≈5 years), existing systems with 10+ years operational history have insurmountable trust advantages—assuming continuous operation and gradual ecosystem accumulation.
Key insight: Competition is possible. Timeline compression is not.
8. Strategic Implications
Path One: Execution Remains Primary
Optimize faster, more expressive execution. Use proofs and stateless techniques for cheaper verification.
Characteristics:
- Execution continues producing canonical truth
- Verification is efficiency layer downstream of execution
- Modular stacks proliferate
- Hardware requirements rise, but proof systems keep verification accessible
Viability conditions:
- Hardware costs drop faster than state growth
- Users accept trusted verification
- Proof systems become arbitrarily cheap
- Atomic composability remains essential
Path Two: Verification Becomes Primary
Ordering defines canonical truth. Execution becomes local, optional activity.
Characteristics:
- Execution removed from trust path
- Composability via message-passing, not atomic execution
- Light clients verify ordering directly
- Systems converge toward integrated security models
Trade-offs:
- Asynchronous composability less intuitive than synchronous
- Developer mental model shift required
- Tooling must be rebuilt from first principles
The Irreversibility Constraint
Execution-first systems reflect Path One. Can add verification features. Cannot invert relationship between execution and truth without starting over (formalized in Appendix A.2).
This is architectural irreversibility.
9. Addressing Counterarguments
9.1 “What if ZK proofs become so cheap that global re-execution is trivial?”
Response: Cost reduction ≠ architectural inversion.
Even with zero-cost proofs:
- Canonical state still derives from executed state roots
- Light clients verify execution proofs, not ordering directly
- Verification is of execution correctness
Verification-first with cheap ZK: similar verification costs, but canonical truth remains ordering, not execution. Execution becomes provably correct but non-canonical—reproducible local computation, not global consensus requirement.
Distinction matters for: composability assumptions, security surface area, protocol complexity (see Appendix A.1 for invariant definitions).
9.2 “Can’t modular stacks approximate without genesis rewrite?”
Response: Modular stacks achieve verification-first properties for applications deployed on top. Do not convert base layer.
Differences persist:
| Property | Modular Stack | Verification-First Base |
|---|---|---|
| Security | Composite (DA + execution + bridges) | Integrated (single consensus) |
| Canonical truth | Execution-derived on L2s | Ordering-derived end-to-end |
| Complexity | Cross-layer coordination, bridge security | Structural simplicity |
Modular stacks: pragmatic response to execution-first limits. Not equivalent to: clean verification-first base layer (see Appendix A.3 for formal counterexample).
9.3 “Why can’t execution-first chains ‘become like Bitcoin’ for general-purpose state?”
Response: Bitcoin’s UTXO enables verification-first for payments because state is minimal and local. Each UTXO independent.
General-purpose state requires:
- Complex cross-contract dependencies
- Multi-contract transaction composability
- Arbitrary computation beyond script validation
“Becoming like Bitcoin” means abandoning:
- Smart contract execution models (EVM, WASM, Move)
- Global state trees (Merkle Patricia, sparse Merkle)
- Atomic composability within blocks
This is equivalent to launching new network.
9.4 “What if hardware advances make full nodes cheap enough?”
Response: Plausible scenario where execution-first remains optimal (acknowledged Section 4).
However, historical trends suggest otherwise:
- State growth unbounded while chains remain active
- Storage costs drop slower than compute (Moore’s Law benefits processing, not long-term retention)
- Bandwidth/latency have physical limits (syncing terabytes imposes time costs even with cheap hardware)
Verification crisis may not materialize if hardware radically improves. But betting L1 architecture on this assumes specific technological trajectory.
Verification-first hedges against opposite scenario: verification costs rising relative to hardware accessibility.
9.5 “Why care about trustless verification if centralized RPC works fine?”
Response: Most users today don’t care. This is the strongest counterargument.
Centralized infrastructure (Infura, Alchemy, QuickNode) is fast, reliable, convenient. If users satisfied with trusted verification, architectural distinction becomes practically irrelevant.
Where this breaks down:
- Censorship: Centralized providers can be compelled
- Systemic failures: Infrastructure consolidation creates single points of failure
- Regulatory pressure: Governments may target gateway providers
- Philosophical consistency: “Decentralized” systems requiring trusted verification undermine their value proposition
Verification-first matters most when trustlessness is non-negotiable. For mainstream users satisfied with convenience over sovereignty, execution-first may remain sufficient indefinitely.
10. Conclusion
The distinction between execution-first and verification-first architectures is foundational and irreversible post-genesis. The choice of what produces canonical truth—execution or ordering—is a genesis-level decision shaping transaction formats, state models, consensus rules, validator incentives, composability patterns, application design.
These constraints are formalized in Appendix A as incompatible invariants that prevent continuous transformations between architectural classes while preserving application functionality.
As of 2026, the architectural quadrant for verification-first base layers with general-purpose state capabilities remains effectively singular in production. Dual-ledger architecture enabling light-client ordering verification without global execution, while supporting general-purpose state through local account-chain execution, represents an occupied but isolated design space position.
Existing execution-first systems cannot migrate into this position without complete reconstruction. Irreversibility stems from incompatible invariants across five dimensions: structural coupling, canonical truth definition, security model integration, economic incentive alignment, composability assumptions.
The open question: Does architectural singularity translate to long-term strategic advantage?
Answer depends on:
- Ecosystem/tooling/developer mental model convergence toward verification-first patterns
- Market beginning to value verification as primary (not execution optimization)
- Scenarios where verification-first offers decisive advantages (censorship resistance, trustless light clients, unbounded state growth) becoming relevant to mainstream users
This paper makes no market predictions. Architectural correctness and market dominance are orthogonal. History shows structurally sound systems can remain underutilized when ecosystem coordination lags protocol capabilities.
Structural claim with confidence: Once a network commits to what produces truth at genesis, that commitment is irreversible. Execution-first systems can add verification features but cannot invert execution-truth relationship. Verification-first systems can add execution layers but ordering remains canonical truth source.
The blockchain industry faces a choice not between better and worse architectures, but between fundamentally different commitments about verification’s role in determining truth. This choice, once made at genesis, cannot be unmade without starting over.
The blockchain industry faces a choice not between better and worse architectures, but between fundamentally different commitments about verification’s role in determining truth.
Falsifiability reminder: This framework is falsifiable via the criteria in Section 3. Discovery of overlooked production systems, successful execution-first to verification-first migrations preserving ecosystem functionality, or modular architectures achieving integrated security equivalence would invalidate core claims.
Appendix A: Formal Definitions
A.1 Invariant Definitions
Definition (Canonical Truth Invariant): Let be the set of all transactions submitted to the network. Let be an ordering function assigning sequence numbers. Let be an execution function producing state .
- Execution-first: where requires global agreement
- Verification-first: and is optional local computation
Definition (Verification Sufficiency): A light client verifies canonical truth if:
- Execution-first: must verify either by re-execution or proof validation
- Verification-first: verifies via cryptographic ordering proofs (signatures, consensus votes, PoW)
Definition (Security Model Integration): Let be the set of security mechanisms.
- Integrated: (single consensus governs ordering and truth)
- Composite: (separate mechanisms for DA, execution, bridging, proof verification)
A.2 Necessary and Sufficient Conditions
Theorem (Verification-First Necessity): For a system to be verification-first, it is necessary that:
- ordering layer such that light clients can verify without executing
- execution model where is local (not required for consensus)
- single security mechanism governing both and canonical truth
Theorem (Verification-First Sufficiency): For a system to be verification-first, it is sufficient that:
- Consensus finalizes only (not )
- Any party can derive state of interest via local replay of
- Light clients verify canonical history via proofs alone
Theorem (Migration Impossibility): Let be an execution-first network in production. Let be the set of verification-first architectural properties. Let be the set of existing application functionalities.
Claim: No continuous transformation exists that preserves .
Proof sketch: Assume preserving . Then must preserve:
- Contract addresses (derived from execution state in )
- Light client verification model (trusts execution in , verifies ordering in )
- Composability semantics (synchronous in , asynchronous in )
- Security assumptions (composite in , integrated in )
- Validator economics (execution-based in , ordering-based in )
Each preservation requirement contradicts architectural inversion:
- Preserving (1) requires execution-derived addresses → contradicts ordering-as-truth
- Preserving (2) requires same verification model → contradicts light client architecture change
- Preserving (3) requires same composability → contradicts async message-passing requirement
- Preserving (4) requires same security layering → contradicts integrated model requirement
- Preserving (5) requires same incentives → contradicts economic realignment
Therefore, preserving . ∎
Corollary: The only path from to is discontinuous: launch new network with genesis-level verification-first commitments.
A.3 Minimal Counterexample to Modular Stack Equivalence
Claim: Modular DA + execution layers satisfy verification-first properties at the base layer.
Counterexample: Let DA layer produce . Let execution layer produce with validity proofs .
Analysis:
-
Canonical application state: , not
- Applications care about executed state on , not mere ordering on DA
-
Light client verification of :
- Must either trust execution, or
- Verify proof of execution correctness
- Cannot verify via alone
-
Security model: where
- DA layer: one security assumption
- L2 execution: separate security assumption
- Bridge contracts: additional trust requirement
- Proof system: cryptographic assumption
Conclusion: Fails both verification sufficiency (cannot derive from alone) and integrated security (composite model with ).
Therefore, modular stacks do not satisfy verification-first base layer properties. ∎
A.4 Falsification Criteria (Formal Statement)
Let be a blockchain system.
falsifies the “empty quadrant” claim if and only if:
Empirical threshold ( material economic activity):
Architectural criteria (all four must hold):
Functionality requirement:
Operational maturity:
As of February 2026:
Discovery of satisfying all criteria would falsify the singularity claim.
Appendix B: Visual Summary
The Blockchain Architecture Matrix
Incompatible Invariants
| Dimension | Execution-First | Verification-First |
|---|---|---|
| Truth source | globally agreed | cryptographically ordered |
| Light client | Verify or trust proofs | Verify directly |
| Composability | Synchronous atomic | Asynchronous message-passing |
| Security | Composite | Integrated |
| Validator economics | Execution throughput rewards | Ordering finality rewards |
Migration Path Analysis
Execution-First System E
│
│ Continuous transformation f?
│
▼
Verification-First System V
BLOCKER: Invariants incompatible (Appendix A.2)
RESULT: No path f exists preserving:
- Contract functionality
- Application composability
- Economic incentives
- Security model
ONLY PATH: Discontinuous (launch new network V')This framework is intended to clarify an architectural distinction, not predict market outcomes. It is designed to remain useful regardless of which networks ultimately succeed.
Falsifiability: Criteria in Section 3 and Appendix A.4 define what would constitute counterevidence. This analysis is subject to empirical refutation.